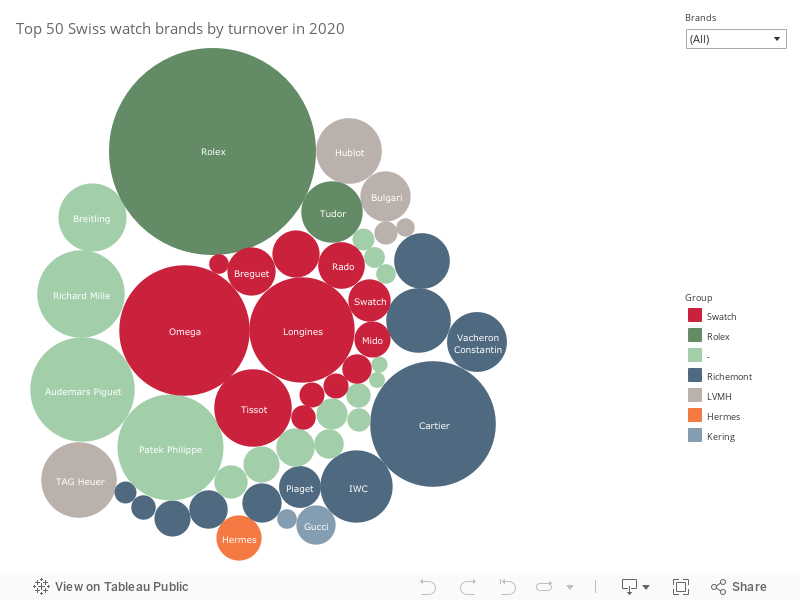
![PDF] Secure Combination of IoT and Blockchain by Physically Binding IoT Devices to Smart Non-Fungible Tokens Using PUFs | Semantic Scholar PDF] Secure Combination of IoT and Blockchain by Physically Binding IoT Devices to Smart Non-Fungible Tokens Using PUFs | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/7d45405ca7a2c351722e798d1774b608b668a29a/8-Table3-1.png)
PDF] Secure Combination of IoT and Blockchain by Physically Binding IoT Devices to Smart Non-Fungible Tokens Using PUFs | Semantic Scholar
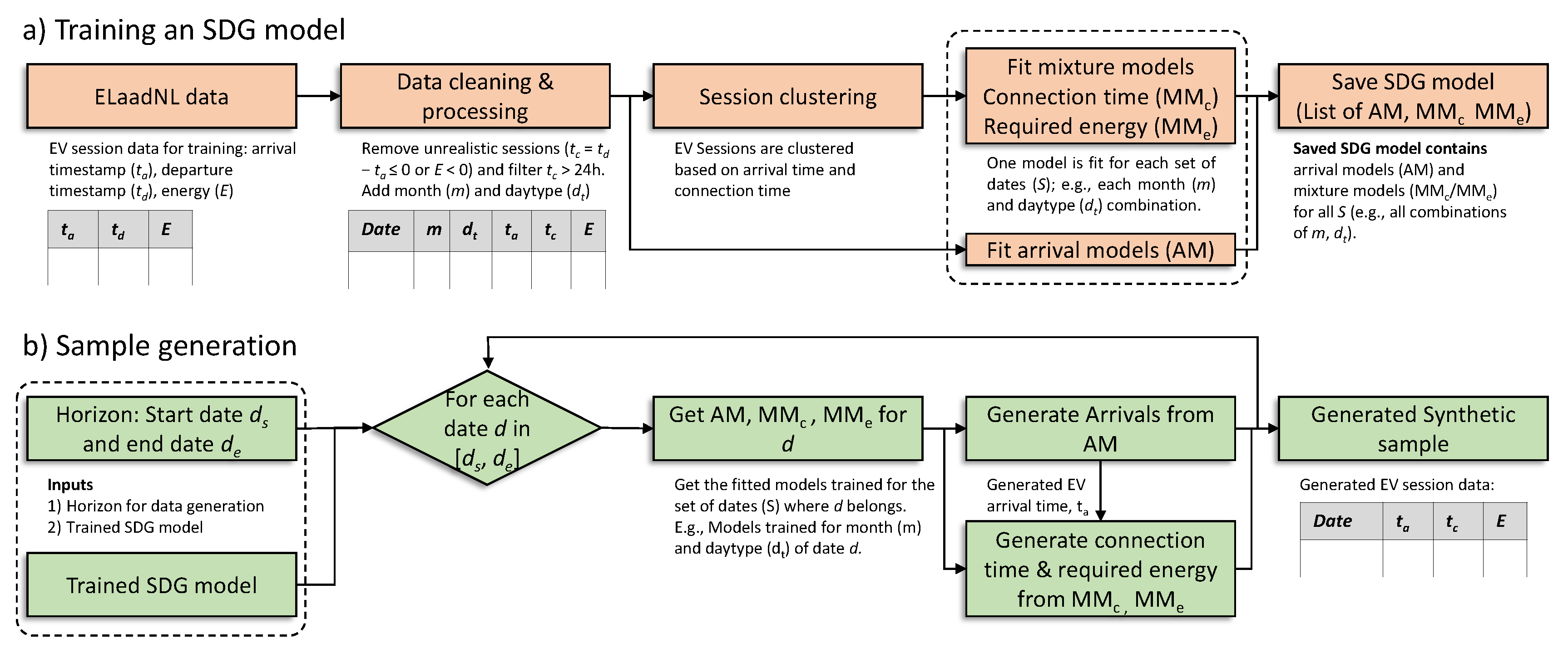
Energies | Free Full-Text | Synthetic Data Generator for Electric Vehicle Charging Sessions: Modeling and Evaluation Using Real-World Data
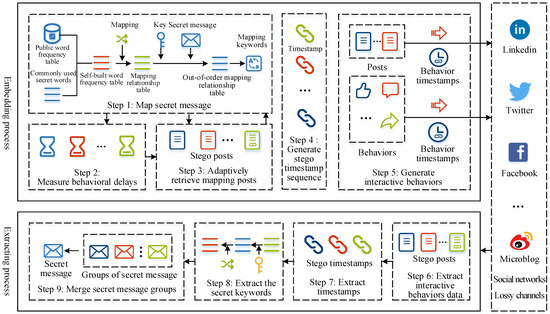
Symmetry | Free Full-Text | A Novel High-Capacity Behavioral Steganographic Method Combining Timestamp Modulation and Carrier Selection Based on Social Networks | HTML

Applied Sciences | Free Full-Text | A Secure Key Aggregate Searchable Encryption with Multi Delegation in Cloud Data Sharing Service

Timing System of the Swiss Light Source Timo Korhonen Paul Scherrer Institute, Switzerland 1. Introduction 2. Components and technology 3. SLS Timing Application. - ppt download

Timing System of the Swiss Light Source Timo Korhonen Paul Scherrer Institute, Switzerland 1. Introduction 2. Components and technology 3. SLS Timing Application. - ppt download